
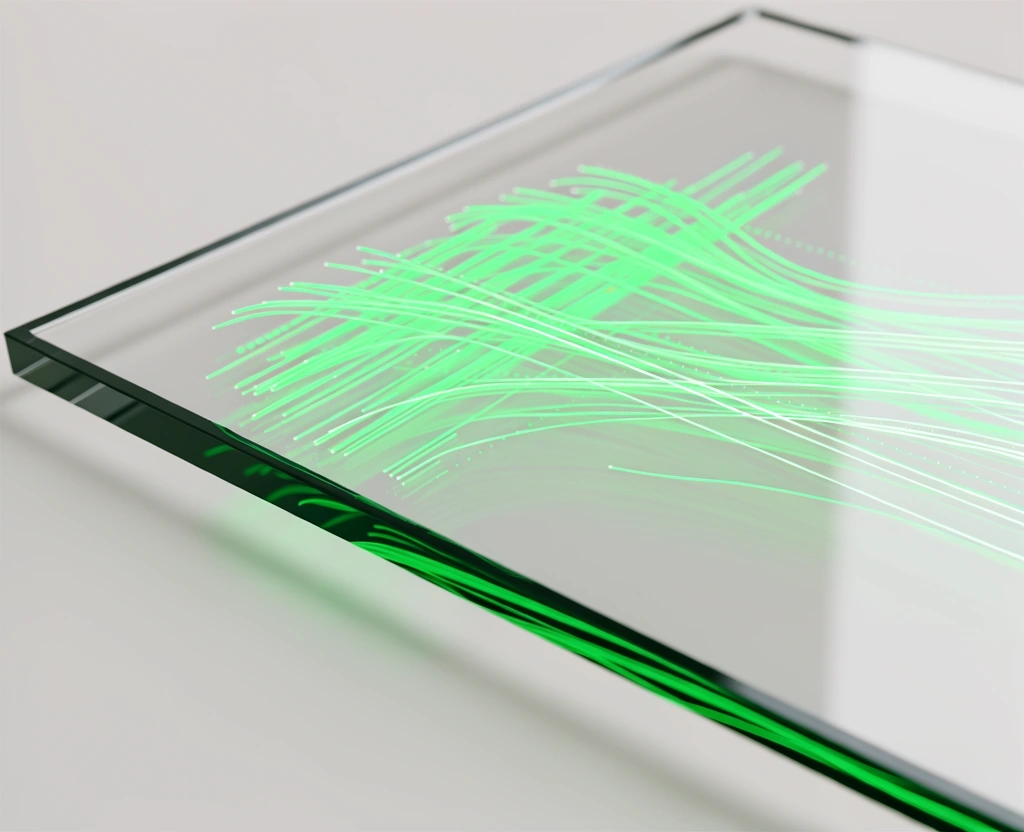
The Architecture of
Data Legitimacy.
Astral Base Trace operates on a foundation of rigorous analytical methodology. We move beyond simple monitoring to provide a deep-layer verification process that ensures every data point in your security ecosystem is authenticated and traceable.
The Multi-Layered Verification Framework
Genuine security requires more than just a surface-level scan. Our analytics engine breaks down incoming base trace data into constituent segments, cross-referencing each against historical integrity markers and real-time threat intelligence.
Origin Authentication
Verifying the hard-point source of every packet to prevent base-level spoofing.
Temporal Consistency
Evaluating time-stamped sequences to detect anomalous latency patterns often indicative of interception.

At Astral Base Trace, we recognize that trace security is not a fixed destination but a continuous state of validation. Our analytics systems are built to withstand the evolving sophistication of data manipulation. By implementing high-frequency integrity checks, we ensure that the information you rely on for critical decisions hasn't been altered in transit or at the source.
We employ a proprietary triple-match methodology. This involves comparing live base trace data against the predicted model, the redundant hardware log, and our global security sensor network. Only when all three points align is data marked as legitimate.
Analytical Rigor
Our operational standards are defined by four core pillars of data integrity.
Integrity Benchmarking
We establish a cryptographic "clean room" baseline for every client environment. Every subsequent base trace is measured against this immutable standard to identify even sub-percent deviations in data structure.
Hardware Resonance
Our analytics look beyond software flags. We monitor hardware thermal and power consumption markers during trace operations to ensure that reporting layers have not been compromised at the OS level.
Cross-Portal Validation
Data legitimacy is verified across multiple isolated nodes. By utilizing a distributed verification model, we prevent a single point of failure within the analytics audit trail.
Exhaustive Auditing
Every analysis result is accompanied by a full evidence chain. This ensures that your security teams can reconstruct the logic behind every legitimacy flag we raise.
Our Commitment to Transparency.
Security standards only work when they are applied consistently. Since our founding in Busan, Astral Base Trace has remained committed to a policy of radical transparency regarding our verification methods. We invite our partners to review our compliance documentation and technical protocols.
Standardized Protocol Questions
Request a Methodology Deep-Dive
Discuss our analytical standards with a senior security architect based in Busan. We are open for technical consultations Mon-Fri, 09:00-18:00.